Logistics and Organization of Online Dating Scammers
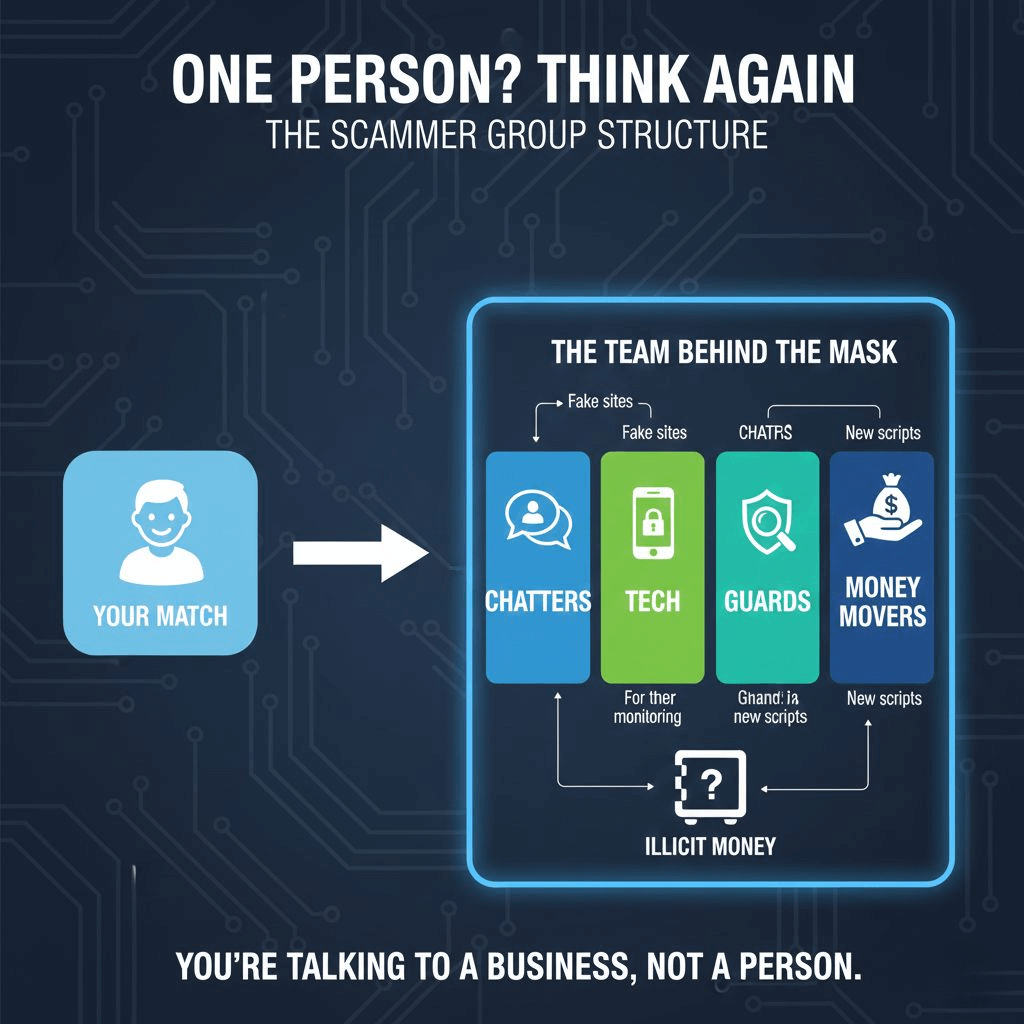
Online dating scams are highly organized, with different roles and technologies involved in executing these fraudulent schemes. Here’s a breakdown of how online dating scam groups work, the roles within the group, and how they manage large-scale operations.
1. The Key Roles in a Scammer Group
Scammer groups operate like sophisticated businesses. Here's a breakdown of the primary roles involved:
| Role | Description | Key Tasks |
|---|---|---|
| Chatting Scammers | Initial contact with victims, engaging in friendly conversation. | Warm up the victim, build rapport, and escalate the conversation. |
| Tech Scammers | Build tools such as VPNs, CRM systems, and AI chatbots to assist the scam operation. | Develop tech solutions for automation, mass communication, and privacy. |
| Guards | Keep scammers "in line" by preventing them from escaping or underperforming. | Monitor and punish scam group members who do not meet targets. |
| Finance People | Handle the money laundering and manage the group's finances. | Wash stolen money and manage financial operations within the group. |
2. How Scammers Operate
2.1 Chat Workflow: How Many People Are You Really Talking To?
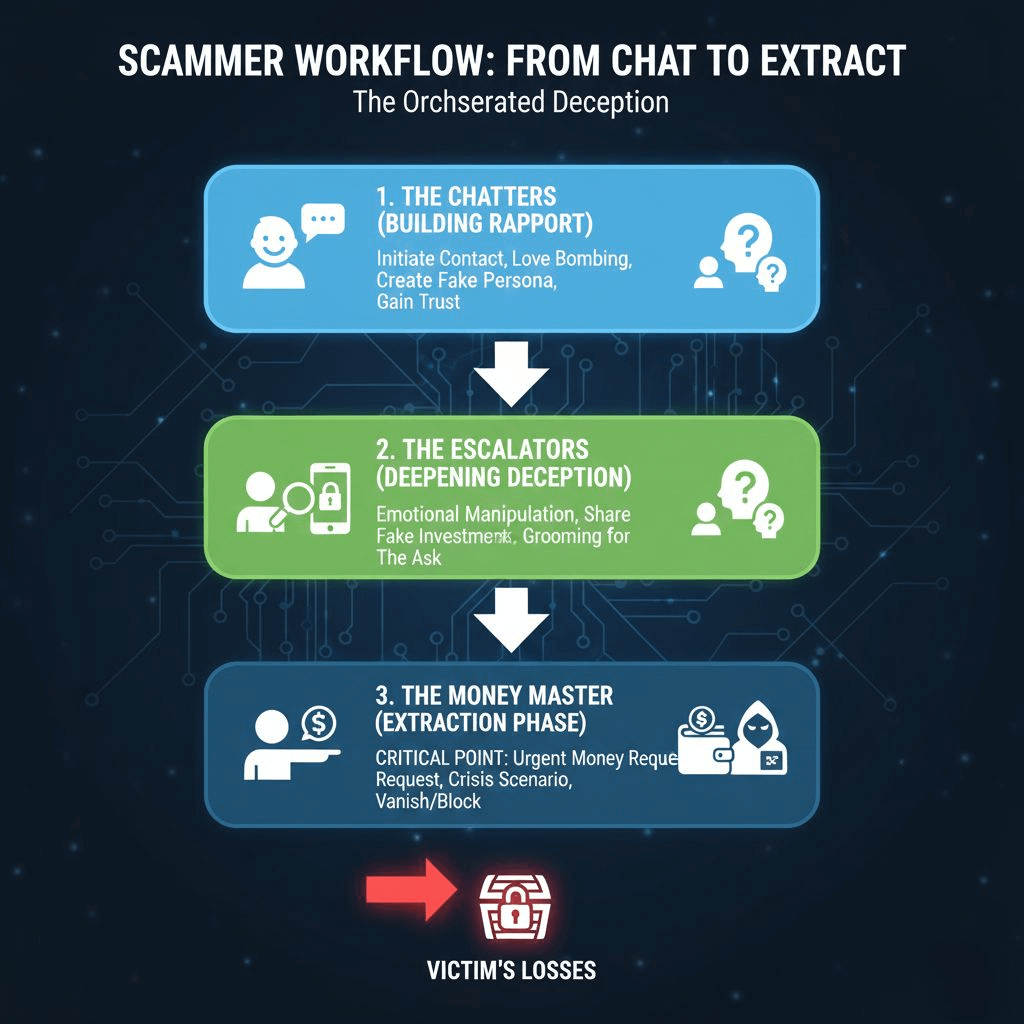
Scammers don’t work alone. Instead, they operate like an assembly line, passing victims between different roles. You may think you are chatting with one person, but you could actually be talking to a whole team of scammers—or an AI.
Initial Conversation: Handled by "chatters" who engage the victim.
Further Engagement: If the conversation progresses, it is passed to another scammer who deepens the emotional connection.
Final Step: The "master scammer" takes over and manipulates the victim to send money.
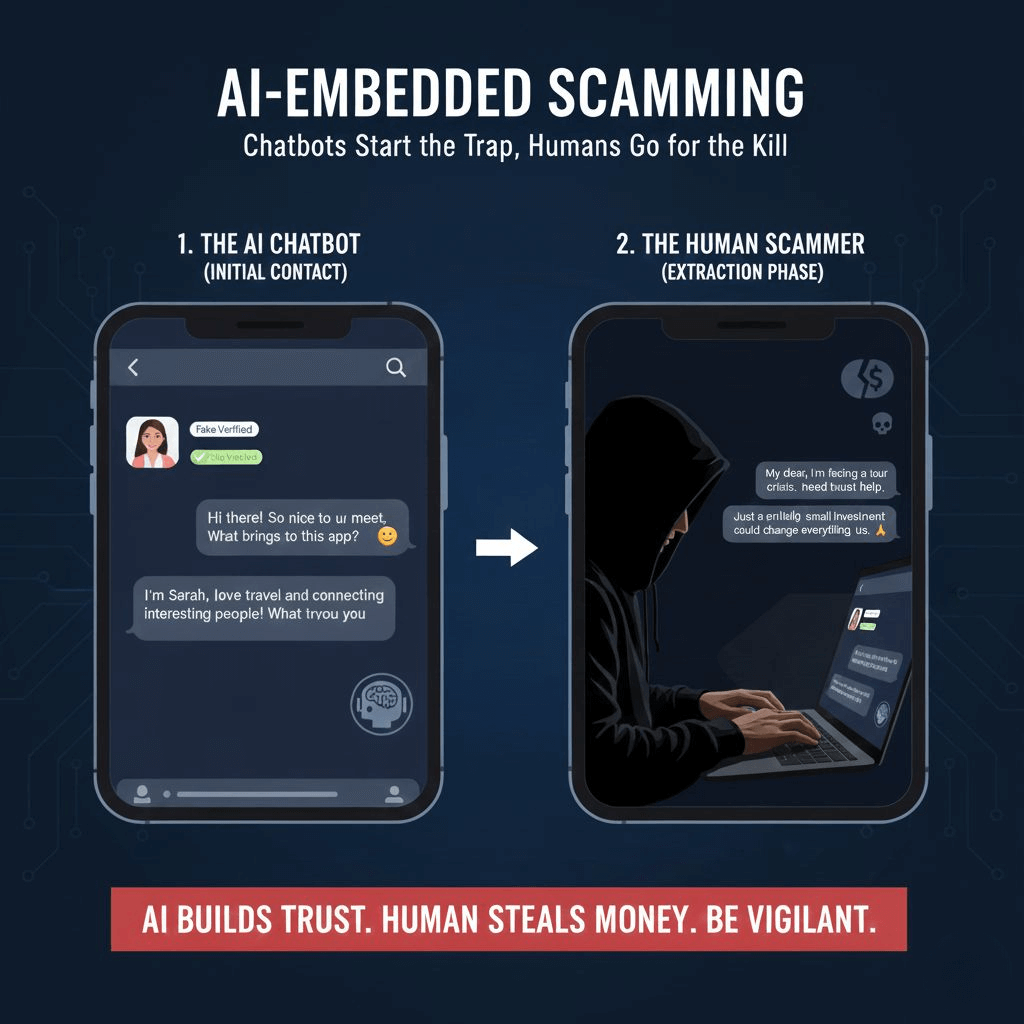
2.2 AI-Embedded Scamming
AI chatbots are used for the first two stages of scamming. These bots can engage in realistic conversations, making it difficult for users to detect that they’re talking to an AI. You might think you’re speaking with a real person, but in fact, it’s likely an AI or a group of scammers working together. However, the final step still involves human scammers to extract money from the victim.
3. Managing a Large Number of Victims
Scammer groups manage thousands of victims at once using Customer Relationship Management (CRM) systems.
3.1 CRM Systems for Scammers
These systems help organize and track the progress of each conversation. The CRM system allows scammers to monitor where each victim is in the scam pipeline and take appropriate action to move the conversation forward.
Automated Workflow: Different scammers perform different tasks, ensuring efficiency.
Mass Communication: Scammers can simultaneously target many victims.
4. Locations of Online Dating Scammers
While many scammers operate from a few well-known regions, they are mobile and can easily shift their operations due to increased scrutiny.
South Asia (Roughly 75% of detected scams): This region is a significant hub for organized scam operations which are located in the countries listed below.
Cambodia (30%), Myanmar (25%), Laos (15%): These countries, located in a triangle in Southeast Asia, have become notorious centers for large-scale, organized online fraud operations, often involving forced labor. Economic conditions, coupled with lax regulations and the presence of organized crime syndicates, create fertile ground for these activities. Scammers here often operate from dedicated "scam compounds" or call centers, running highly professionalized schemes.
Thailand (5%) and Philippines (5%): While also present, these locations show less scam activities compared to their neighbors, mainly for being more stable. However, similar sophisticated operations originate from here.
• Central Africa (roughly 10% of detected scams) Ghana, Nigeria, Central African Republic, Ivory Coast: These nations have long been associated with online fraud, often due to economic disparities and established networks of cybercriminals. The infrastructure for simpler romance type scams is wellentrenched.
• Russia and Ukraine (roughly 10% of detected scams) The geopolitical situation and a strong existing cybercrime ecosystem contribute to these regions being sources of scam activity. Highly skilled individuals, sometimes operating independently or in smaller groups, leverage their technical prowess.
• Turkey and Cyprus (roughly 5% of detected scams) These locations, often acting as transit points or regional hubs, show a smaller but distinct pattern of scam types.
Reference: https://www.onluxy.com/2025-scam-prevention-report.pdf

5. FAQ: Online Dating Scammer Groups
Q1: How do scammers manage to talk to so many victims at once?
A1: Scammers use CRM systems, AI tools, and role specialization to handle thousands of conversations at once. These systems allow them to automate and scale their operations effectively.
Q2: Are all scammers part of large groups?
A2: No, some scammers operate individually, especially in regions like Nigeria and South Africa. However, large groups are more efficient and can scam more people.
Q3: Can AI really convince users that they’re talking to a real person?
A3: Yes, modern AI chatbots can mimic human conversation so convincingly that many victims can’t tell they’re interacting with a bot.
Q4: Why do scammers ask to move to another platform like WhatsApp?
A4: Scammers push users to other platforms like WhatsApp because these platforms don’t have the same monitoring or reporting features as dating apps. This helps them avoid detection.
Q5: How can I protect myself from these scams?
A5: Always verify the person through a live video call on the dating app. Never share personal or financial details, and be cautious if someone pressures you to leave the platform.
6. Conclusion: The Growing Threat of Online Dating Scams
Scammer groups are highly organized and increasingly sophisticated. With specialized roles, AI tools, and CRM systems, they can deceive thousands of people around the world. Understanding how these scams operate can help you protect yourself and avoid falling victim to these fraudulent schemes.
Always stay vigilant, request verification, and report any suspicious activity to the platform immediately.
7. Final Safety Checklist
✅ Stay on the dating platform until you verify someone's identity
✅ Don’t share personal information too early
✅ Avoid moving conversations to other platforms
✅ Report suspicious activity immediately
Reference: